A CAA record is a special type of DNS record (think TXT or CERT) that allows domain owners to authorize specific third party vendors to issue SSL certificates on behalf of their domains.
CAA records are part of a series of schemes aimed at improving the security of the SSL certificate system. If, for example, NS1 wanted to use name.com to get an SSL certificate for newportal.ns1.com, we could add a CAA record that specifically granted name.com authorization to issue certificates for *.ns1.com. Then when we go to purchase the certificate, name.com would know with certainty that they are allowed to issue the cert on our behalf.
The CAA record prevents any other Certificate Authority from issuing an SSL certificate for our domain. Only the CA(s) we authorized in the CAA record, name.com in this example, can issue an SSL certificate for *.ns1.com. The CAA record becomes one more piece that makes up the whole of your online website security measures.
NOTE: This is an optional record type. As a domain owner, there are no requirements for you to have a CAA record.
The following graphic shows an example of how CAA records work in the DNS hierarchy.
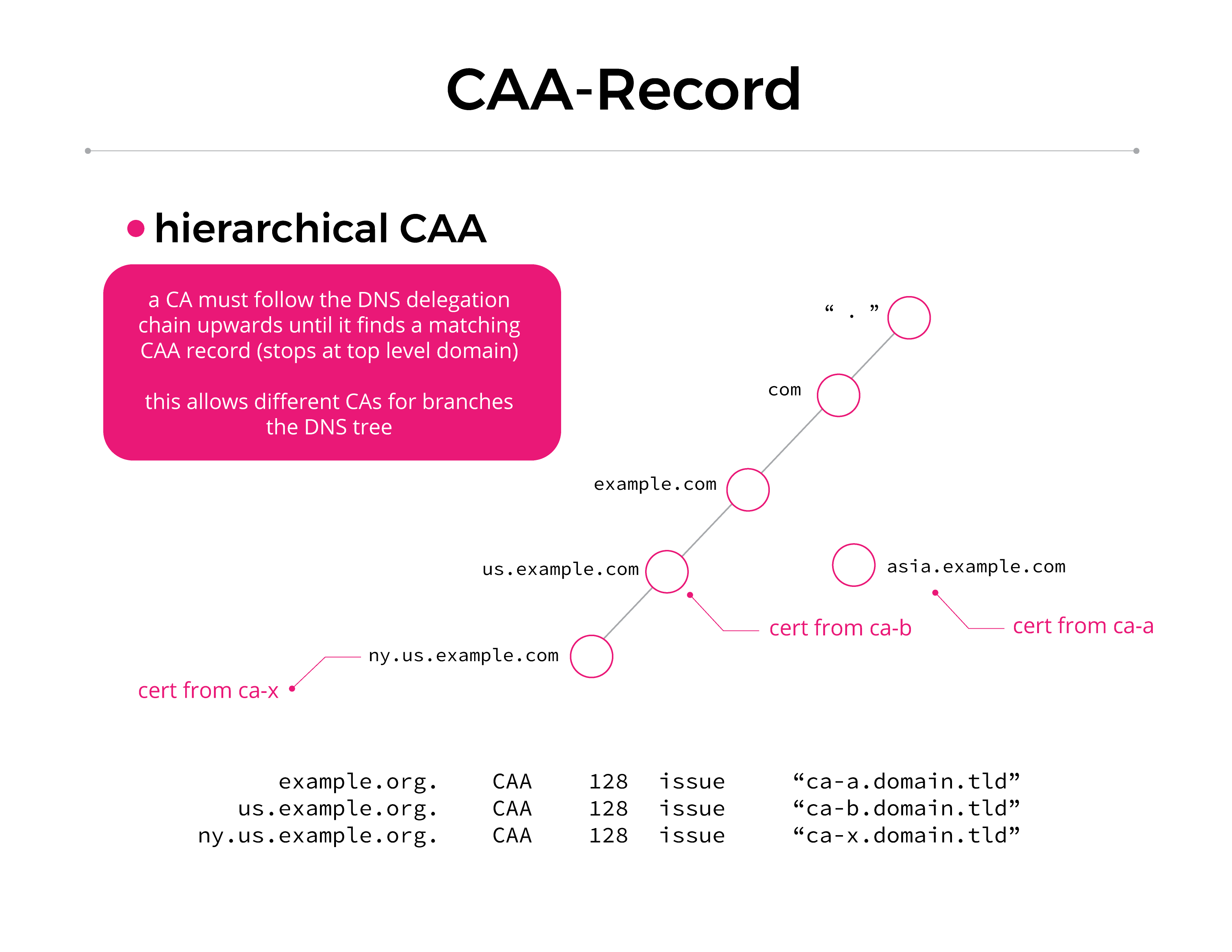
From the graphic: a CA must follow the DNS delegation chain upwards until it finds a matching CAA record (stops at top level domain). This allows different CAs for branches in the DNS tree. (Men&Mice)
To add a CAA record to your Managed DNS account with NS1, you first contact your CA provider and request their identification string. You can then create your CAA record in NS1’s portal according to the instructions in our KnowledgeBase article. Add the CA’s identification string into the CAA record parameters in your domain. This limits who can issue your domain certificates.
As of September 2017, CAs are required to check for the presence of a CAA record and, if one is found, verify that they are authorized prior to issuing certificates for this domain. If a CAA record is not present, the CA can issue a certificate for the domain.
For more information on the CAA record type, see RFC 6844.